Turn On The Lights For Your Enterprise Endpoints, Finally.
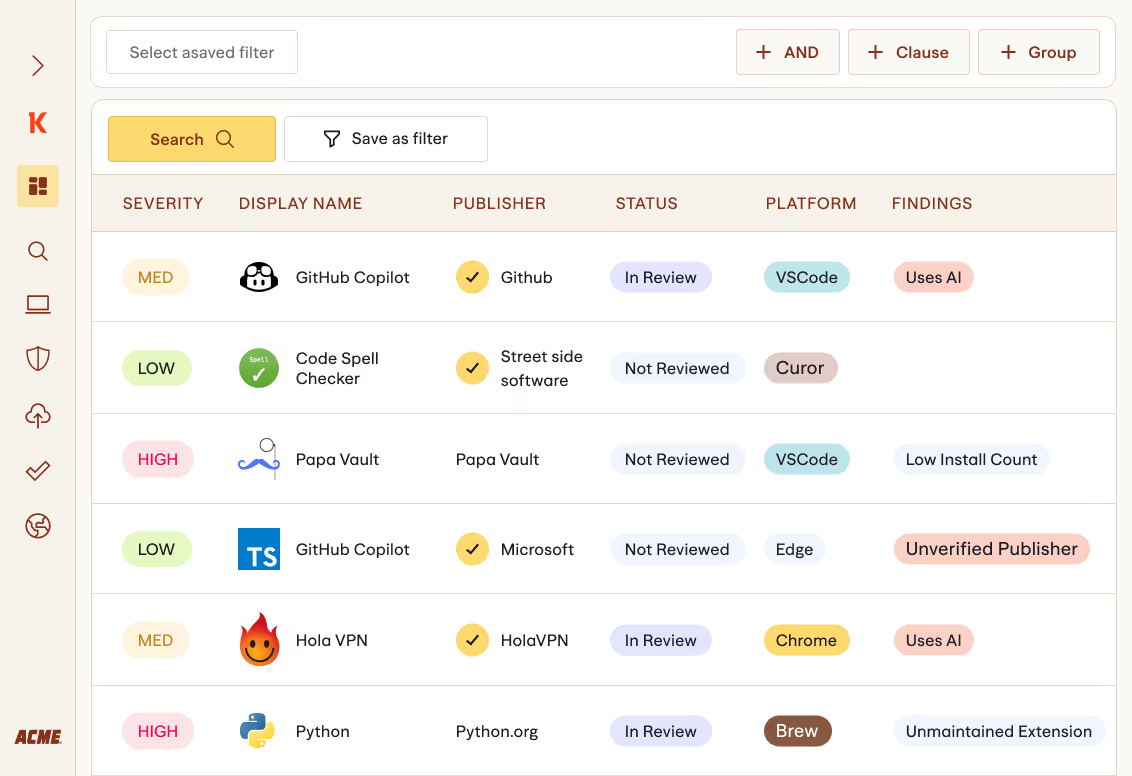
Discover all software applications, both binary and non-binary, that exist on your endpoints, gain critical risk insights, and govern by removing or reconfiguring risky, malicious, or non-compliant software.

Stop putting out fires, and regain control of your endpoints.
Koi’s Endpoint Security Posture Management (ESPM), a world's first, maps out all software in your enterprise, from applications, to code packages, to AI models, to OS packages and drivers, to extensions and containers.
Inventory them all, whether a binary installed or portable applications, or a non-binary software like code packages, OS packages, extensions, AI models, MCPs, or containers.

Get rid of DLL inventories, Koi gives you full visibility to all applications that exist in your environment, whether running or not.

Empowering you with intelligence & knowledge to make smart decisions and wisely control your endpoints application attack surface

Remove or reconfigure malicious, risky, or non-compliant software in seconds, across hundreds of thousands of endpoints.

Wings™ checks what software is actually
made of, extensively.
scanning
Wings™ completes a full scan of all marketplaces every hour.
intelligence
We assess the vendor based on all their previous publishings.
software comparison
Our LLM scans the actual code behind the software.
on actual code
That includes enriching and sandboxing the code.
Wings™ assigns the software a risk score based on detected indicators.
with new versions & changes
Because software isn’t static.
Endpoint Security Finally Done Right.
%20(1).png)
.png)
.png)
Automatically uncover and catalog all non-binary and binary software in your IT environment.
Wings, our agentic AI risk engine, correlates code diffs, runtime behavior, ownership changes, update channels, network egress, and install source to detect malware, impersonation, and policy drift in real time.
Define org-wide rules by user, group, and asset sensitivity. Approvals, cooldowns, and allow/block lists enforced automatically
Detect malware, sideloading, and risky update channels post-install. Alert owners and stop propagation.
.png)
%20(1).png)
.png)
.png)

Ready to secure every install?
Watch a 3-minute demo
See how Koi secures all software in your IT environment—from packages to add-ons and extensions—making marketplace risk visible and actionable.

Get access
Enter your work email to watch the demo.

.png)



